Dahua is one of the world’s largest CCTV manufacturers and is quite popular worldwide, including in the United States.
The company is a Chinese private-owned entity that claims no affiliation with the Chinese government, but that has not stopped the US government from banning Dahua and their OEM from federal CCTV projects.
A large number of American companies and CCTV sellers buy Dahua OEM security equipment and resell them using their own brand name, logos, and models, most of the time purposely hiding the fact that the cameras are Dahua.
There are a few ways how to tell if a camera or a security device is Dahua OEM: product documentation, inspecting the firmware, checking the camera’s motherboard, the interface, the shipping record, etc.

Which companies sell Dahua OEM products
In this article, we’ve listed all the known companies that sell Dahua OEM products, usually under their own brand names and logos.
A few of these companies have stopped selling Dahua and moved to other OEMs. The Dahua OEM (rebranded) sellers are listed alphabetically (most of them sourced from IPVM, a few more added by SCC).
- 2M CCTV
- Activecam
- Advidia
- Altoros
- Amcrest
- Ameta
- Ascendent
- Backstreet Surveillance
- Bosch (a few of their cameras and NVR models)
- BV Security
- CCTV Security Pros
- CCTV Star
- CP Plus
- Dax Networks
- DH Vision
- eLine
- Eastern CCTV
- ENS Expose
- Lorex
- Gess Technologies
- GSS
- Honeywell (a few of their product lines)
- Heivision
- IC Realtime
- Ikegami
- Inaxsys
- IndigoVision
- Infinity CCTV
- Innekt
- Intelbras
- KBVision
- Lumixen
- Maxron
- Montavue
- Oco
- Optiview
- Panasonic (in certain countries only)
- People Fu
- Platinum CCTV
- RedSpeed
- Rhodium
- RVI
- Saxco
- SavvyTech
- Security Camera King
- Space Technology
- Speco
- ToughDog
- Unisight
- VIP Vision
- Watchnet
- Winic
- Zuum
Usually, these companies purchase bulk product lines from Dahua and stamp their own logos, brand names, models, and interface color schemes.
Most of the time they try to hide the original manufacturer or make it difficult for the end-user to trace the camera’s origin. Sometimes they will modify the firmware as well, or try to customize it.
Former Dahua OEM sellers
After Dahua was banned by the United States government, many sellers dropped them and moved to other OEMs such as Uniview, Hikvision, TVT, Raysharp, etc. Some even went out of business or merged with other companies.
- ADT (their residential line used to be Dahua OEM)
- Annke (move to Hikvision OEMs)
- Aposonic
- BCS
- Cantek
- Dotix
- DVR Unlimited
- Eyenor
- FLIR
- HQVision
- Legrand
- Norden
- Q-See
- Raster
- Riva
- SecurityTronix
- Techpro
- Tyco Holis
- Tyco Illustra EssentialsUra
- Watashi
How to tell a Dahua OEM
There are a few ways to tell if a security product is Dahua OEM.
Similar Interface
Even though the OEM resellers try to hide the fact the equipment is made by Dahua, there are still similarities in the interface that can’t be hidden.
These clues are the web interface layout, the login screen, user interface and layout, the color scheme, the placement of the settings, etc.
So, if you compare the interface of a Dahua brand name camera with one from an OEM seller, you’ll notice that interface is quite similar. An example is shown below, an IC Realtime interface and the original one from Dahua (notice how similar they are).

Same Configuration Tool
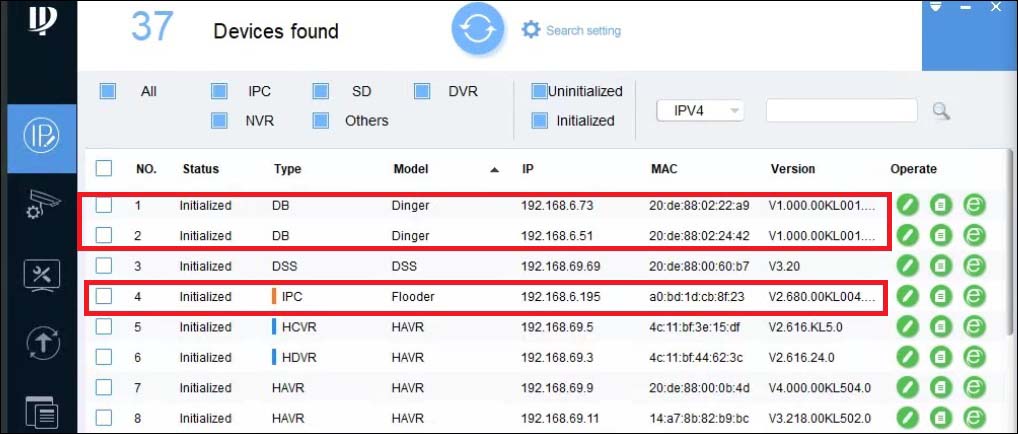
All Dahua OEM models can be discovered by using Dahua’s scanning tool (called IP Config tool). Simply run the software on the laptop, scan the network, and no matter what brand the device has, if it’s Dahua, it will get listed on the tool.
Below is an example, an IC Realtime device is detected by Dahua’s IP config tool. That’s an indication the device is Dahua OEM.
The MAC address
You can look up the MAC address of the OEM device and find out if it’s reported as Dahua-made equipment. For example, you can use this tool MAC OUI to lookup (from Wireshark) the MAC address.
However, some OEM resellers are able to hide or manipulate the MAC addresses in order to mask the original manufacturer.
Model number on the motherboard
The OEM resellers use their own models and logos for the equipment they sell, but still, if you open up any device (camera for example) you’ll find the model number inscribed on the motherboard.
Simply google it and you should find out that, in fact, it’s a Dahua OEM.
Dahua Security Vulnerabilities
Dahua-made security devices are famous for their repeated major cybersecurity vulnerabilities in the past few years. So far, the following vulnerabilities have been found (according to IPVM):
- Wiretapping vulnerability, 2019: A security researcher discovered that audio streams could be accessed without authentication in Dahua and OEM models. In other words, an unauthorized party was able to attack the camera and listen to its microphone, even when the option was disabled on the camera’s settings.
- Exposed credentials, 2017: Vulnerable Dahua cameras and DVRs or NVRs contained an unsecured configuration file with the device’s username and password. Hackers could remotely access these devices and retrieve their credentials.
- Hardcoded backdoor, 2017: This software vulnerability allowed unauthorized parties to gain admin access to the camera, basically, fully taking over the camera’s feed or the DVR/NVR.
If you’re using any of the products from the companies listed in this article, make sure to update their firmware to the latest version, especially if the equipment is manufactured by Dahua.



