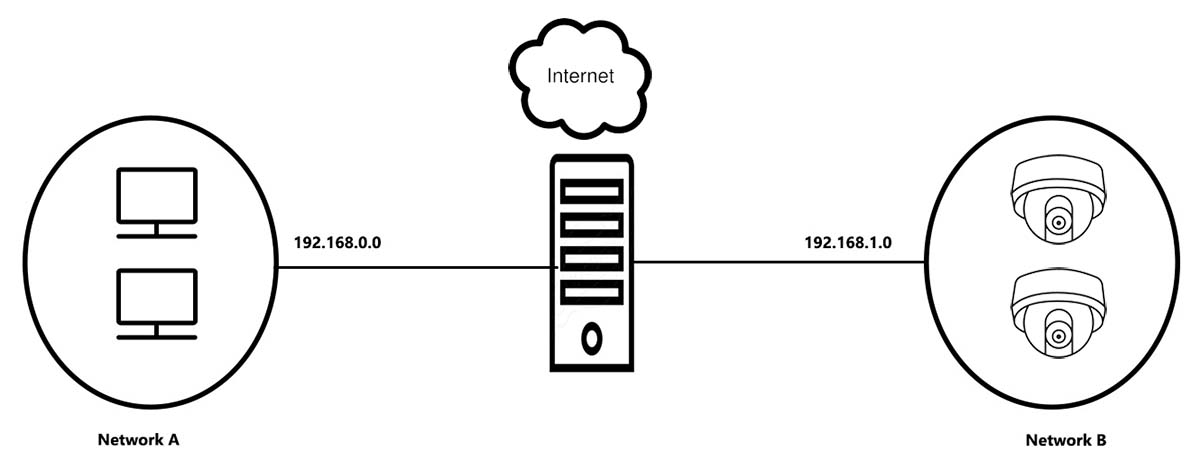
It’s a common question: Is it better to place the IP security cameras in a separate network? There are many reasons why you should group IP cameras on a separate network and by doing so you’ll increase the security and the performance of the system.
To cut it short: Yes, it’s recommended to group all your IP security cameras on a separate local network. This way, the cameras will be in a different security zone, increasing the overall performance, and safety and reducing the risks of getting hacked.
The information gathered by security cameras is compressed and then transmitted (wired or wirelessly) over the network to a network video recorder (NVR) which stores the videos on its internal hard drives.
One of the advantages of IP cameras is that they generate high-resolution footage and use advanced data encryption to reduce the risk of hacking or getting compromised.

Hacked IP cameras can expose all enterprises such as financial institutions, buildings, stores, and factories, to severe security issues that may hinder the work or even shut the whole thing down.
The IP cameras can be accessed remotely and hackers can use this to their advantage. In this guide, we will list the reason why you should “hide” your IP security camera in a separate network.
Reasons to isolate IP security cameras in a separate network
Accessing a separate IP cameras network is safer and easier to manage
First things first, if you isolate the IP cameras on a separate and dedicated network, then the cameras will not impact the other systems that operate on the main network.
Enterprise networks (or even residential ones) may contain multiple smart devices and if you add IP cameras (let’s say 10, 15, 20), then the network may get congested and the overall performance will decrease.
Moreover, by isolating the IP cameras in a separate network, you further limit who accesses these cameras. Let’s say the cameras are connected to the main network, this means the cameras are seen and possibly accessed by anyone who can access the main network.
But, if you group these cameras on a separate network, then the cameras cannot be seen/scanned through the main network. Only the people who manage the IP security within the company can access and locate these cameras.
In other words, when placed on a separate network, you drastically reduce the number of external elements that “see” the cameras. At last, the IP cameras will not be directly exposed to the outside and only authorized personnel will be able to log into them.
Easier to sport unusual activities on the network
It’s easier to track usage, suspicious activities, unusual patterns, and other parameters when you have a number of limited users accessing your network. The more users, the more difficult it gets to properly track suspicious behavior.
If a hacker accesses a security camera system, the system’s admin will notice unusual patterns such as file transfers, ongoing and outgoing bandwidth changes, and other issues that can be investigated further.
When the cameras are placed in a separate network, it’s much easier to notice these telltales compared to having the security system in a regular crowded network.
Better Performance
By segregation the IP cameras on a separate network, you ensure that the camera’s high traffic won’t impact the normal LAN.
When using all the devices on the same network without separating the devices into sub-networks, then there may be bandwidth issues, especially will high-resolution cameras that transmit a lot of data to the recorder.
Depending on the configuration, by placing the IP cameras on a separate network, you may cut them from the internet and thus remove the risk of them sending sensitive information over the Internet or being hacked.
How to isolate IP security cameras in a separate network?
A separate local IP camera network operates on Layer 2. Below is shown how the devices communicate:
- Layer 1 (Physical Layer): data bits over physical mediums
- Layer 2 (Link Layer): data frames between connected nodes on the physical layer
- Layer 3 (Network Layer): addresses routing and traffic control on a multi-node network.
VLAN configuration for security camera systems is very important to protect the IP cameras against unauthorized access and also to separate the security camera system from other devices that are connected to the local network (LAN).
You may wonder, is VLAN and subnet the same thing? At a high level, subnets and VLANs are analogous in that they both deal with segmenting or partitioning a portion of the network.
However, VLANs are data link layer (OSI layer 2) constructs (check the list above), while subnets are network layer (OSI layer 3) IP constructs, and they deal with different issues on a network.
Setting up the VLAN may require a bit of network knowledge but it’s totally doable if you know how to research issues on Google.
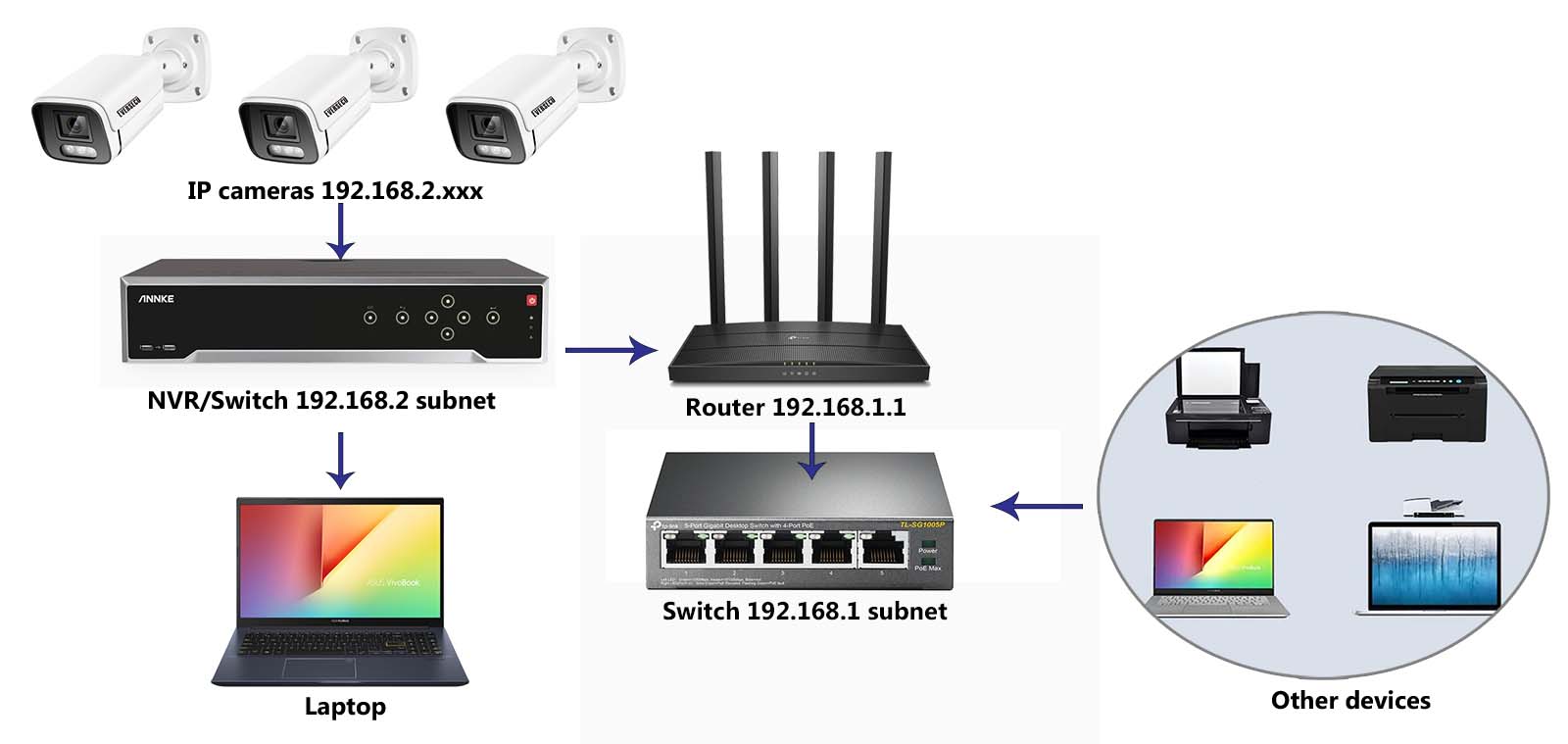
Below is shown the scheme of how you can connect the surveillance cameras on a separate network using basic network isolation.
Note the subnet’s IP addresses for other groups. The IP cameras are on a different network from the other devices on the network (computers, printers, laptops, phones).
Configure the subnets
The important thing that you need to know is that when running multiple LANs, each of them operates on a separate subnet.
The subnet address is defined by the first three numbers, while the IP address is four numbers. For example, if the camera’s IP address is 192.169.1.100, then the subnet for this segment is 192.168.1.
Most routers are set on DHCP mode, which means the router will assign an IP address to the devices automatically and place them on the main subnet mask.
If the router is 192.168.1.1, then newly connected devices on the network will get an IP address such as (for example) 192.168.1.100. Note that they are in the same format.
On the other hand, the IP cameras can be grouped on a different subnet which should be different from the main one. If the router’s subnet is 192.168.1, then the camera’s subnet can be 192.168.2.
In this scenario, the camera can’t utilize their DHCP service, which means you need to set their IP addresses and settings manually and ensure they match the subnet’s format.
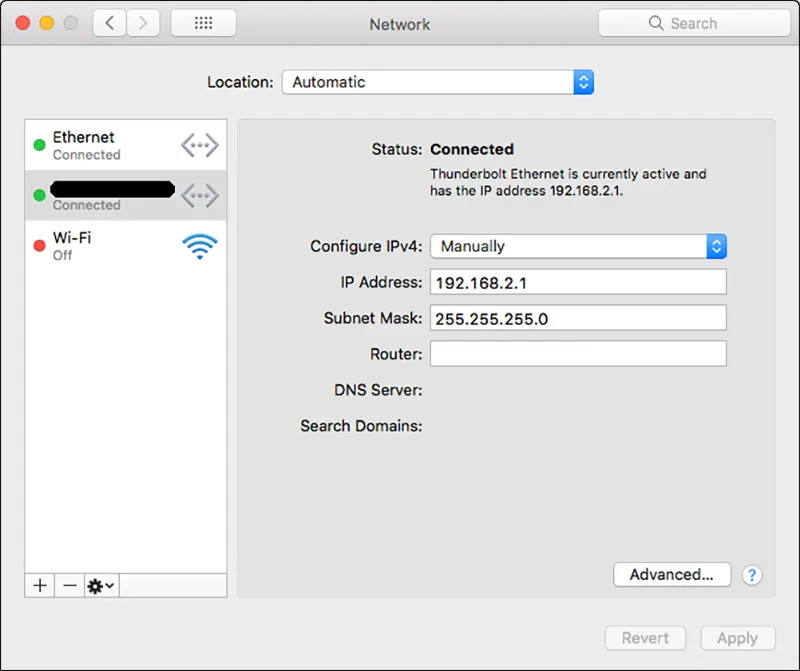
Let’s say you’re using 192.168.2 subnet for the cameras. Connect these cameras to a PoE switch and then connect a laptop on the same switch/network. Change the laptop’s IP address to 192.168.2.1 and set the subnet mask to 255.255.255.0. Leave the router’s IP address empty.
The pictures below show the settings for Windows:

This is for Apple (Mac) devices.
Configure the IP cameras
Next, you should configure the cameras manually to match that of your separate network. This depends on the camera model and brand, but the logic is the same regardless of the type of camera you’re deploying.
Follow these steps:
Connect the cameras to the local network using a PoE switch. The laptop must be connected to the same switch/network as well.
Now it’s time to find out the current IP address of the camera. For this, you can use a generic IP scanner, although we’d recommend the one made specifically for your camera brand. Each brand uses its own IP Camera Finder.
For example, Hikvision uses the SADP tool. This article lists all the IP scanners for each camera model. Run the tool, and all the IP cameras found on the network will be listed.
Select the camera and then (using the tool’s functions) change the IP address for the camera to match that of the chosen subnet.
If the subnet is 192.168.2, then you can assign to the camera an address such as 192.169.2.x, where x is a unique number between 2 and 254. Once you do so, the camera will no longer be accessible from the main LAN (which is 192.168.1).
Also, keep in mind, there’s no need to assign a router address or DNS address on the camera. If it requires it, just add 192.168.2.254 or all zeros.
Connect the camera to the other (camera’s) switch as shown on the diagram above (beginning of this section).
Now the cameras are on a separate network (192.168.2) and cannot be accessed or seen from the main local network. This method makes the security camera safer and increases the overall performance.
Conclusion
IP camera surveillance systems need to be designed in a way that removes the potential for interference with other network subnets and reduces the chances of getting hacked. One method to do this is by placing the camera on a separate network (subnet).
For security reasons, we’d always recommend limiting the number of users who can access and see the camera on the network and one safe way to achieve this result is by placing the cameras on a separate and isolated network.
Lastly, you may use NVRs with a built-in PoE switch which by design places the cameras on a separate network that can’t be accessed individually (such systems are shown here).






